TLS Support on Network Load Balancer
Prior to this launch, you faced the following difficulties – your application performance suffered as encryption/decryption is compute intensive where you needed to provision extra capacity to your backends to handle TLS termination. Apart from that, managing certificates on your backends became complex as your applications grew. Applying security patches or upgrading TLS stacks on your backends was hard and time consuming.
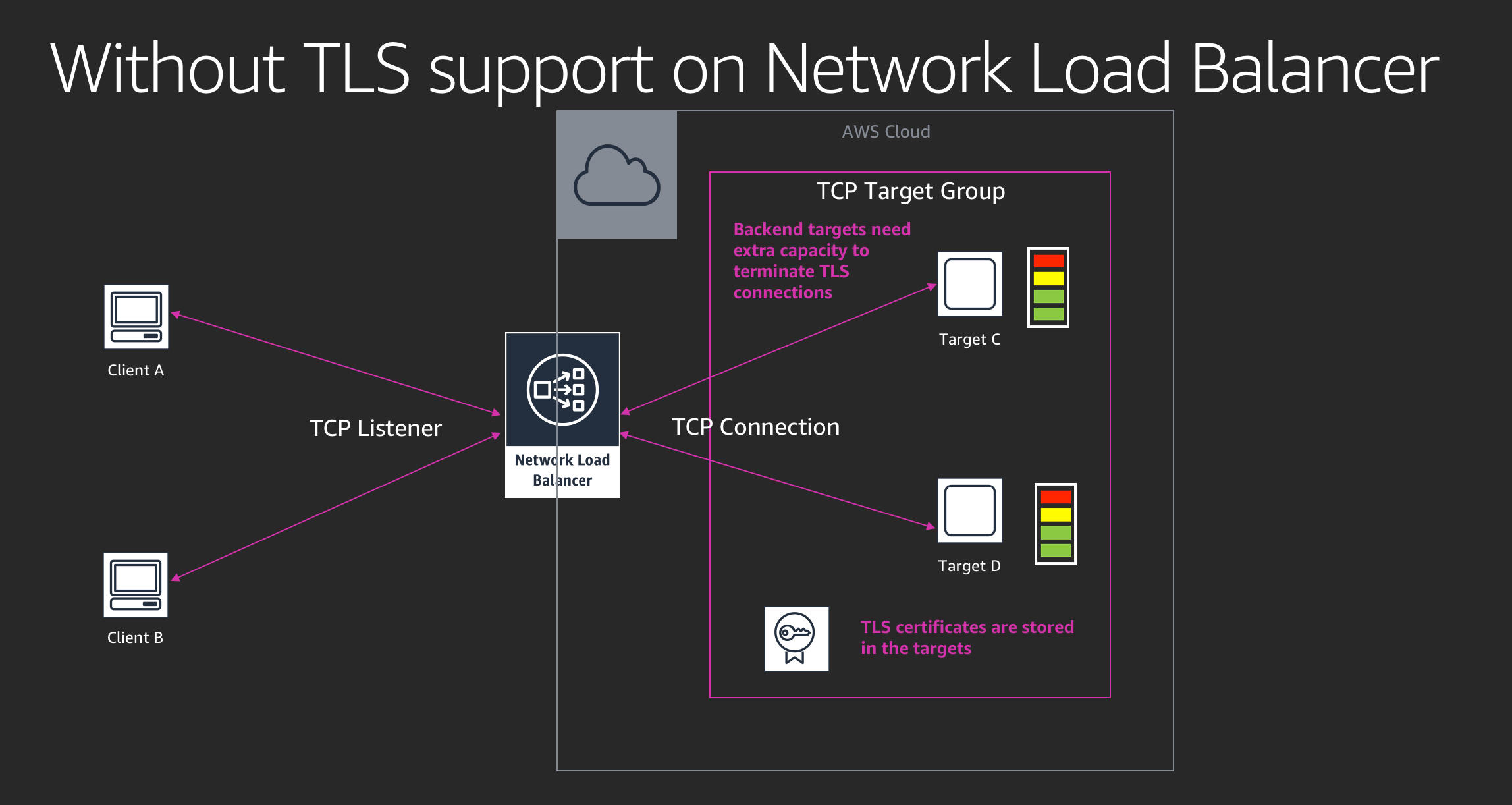
TLS Termination support on NLB will address these challenges. By offloading TLS from the backend servers to a high performant and scalable Network Load Balancer, you can now simplify certificate management, run backend servers optimally, support TLS connections at scale and keep your workloads always secure. Network Load Balancer also offers predefined security polices, which ensures that secured ciphers and protocols are being negotiated between the user and Network Load Balancer.
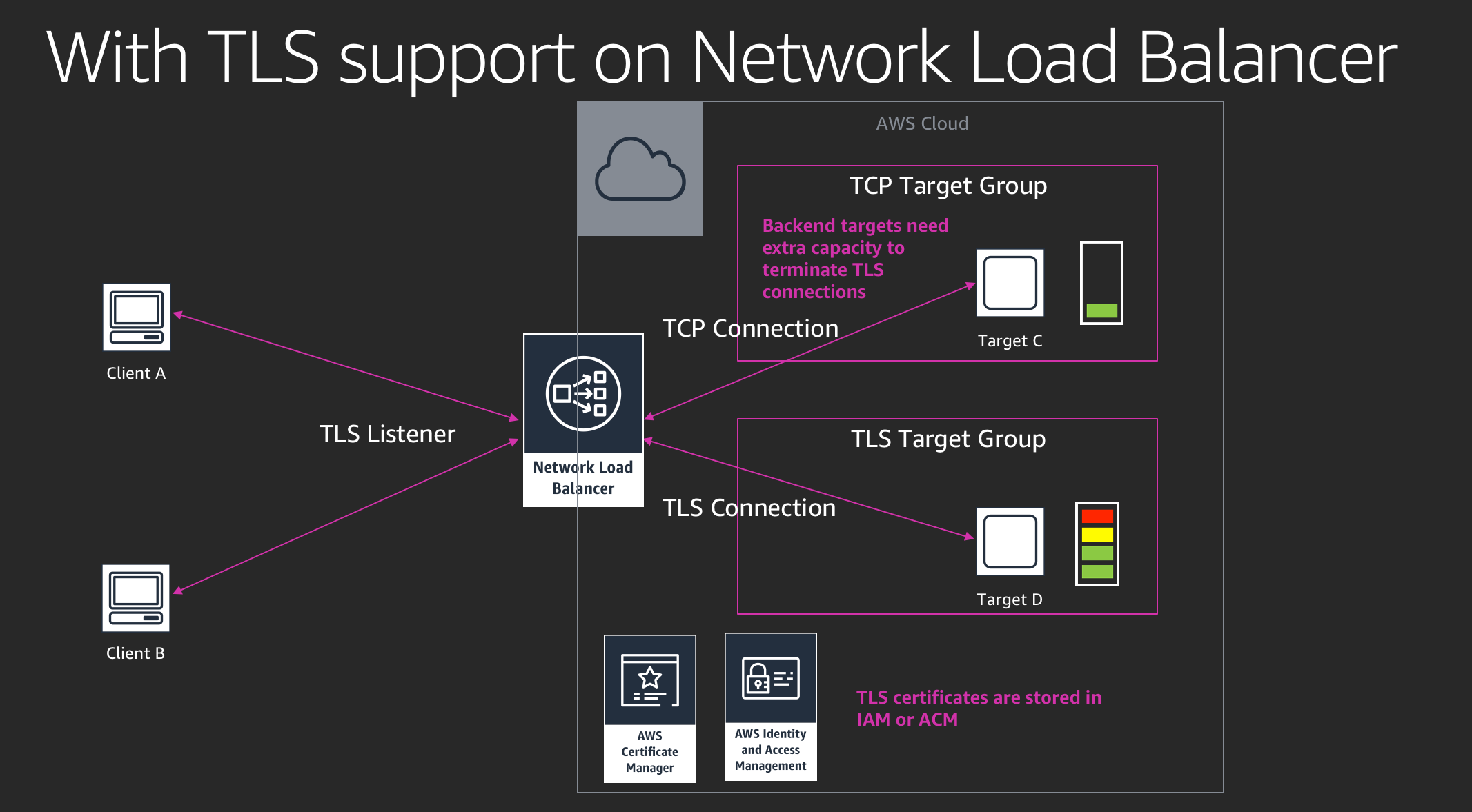
By negotiating the optimal cipher, protocol, and key exchange algorithm with clients on behalf of your backend servers, your site/service can achieve PCI, and Fed Ramp compliance as well as a perfect TLS score. TLS Termination support on Network Load Balancer is also integrated with PrivateLink, which allows you to securely expose your service to your partners in AWS.
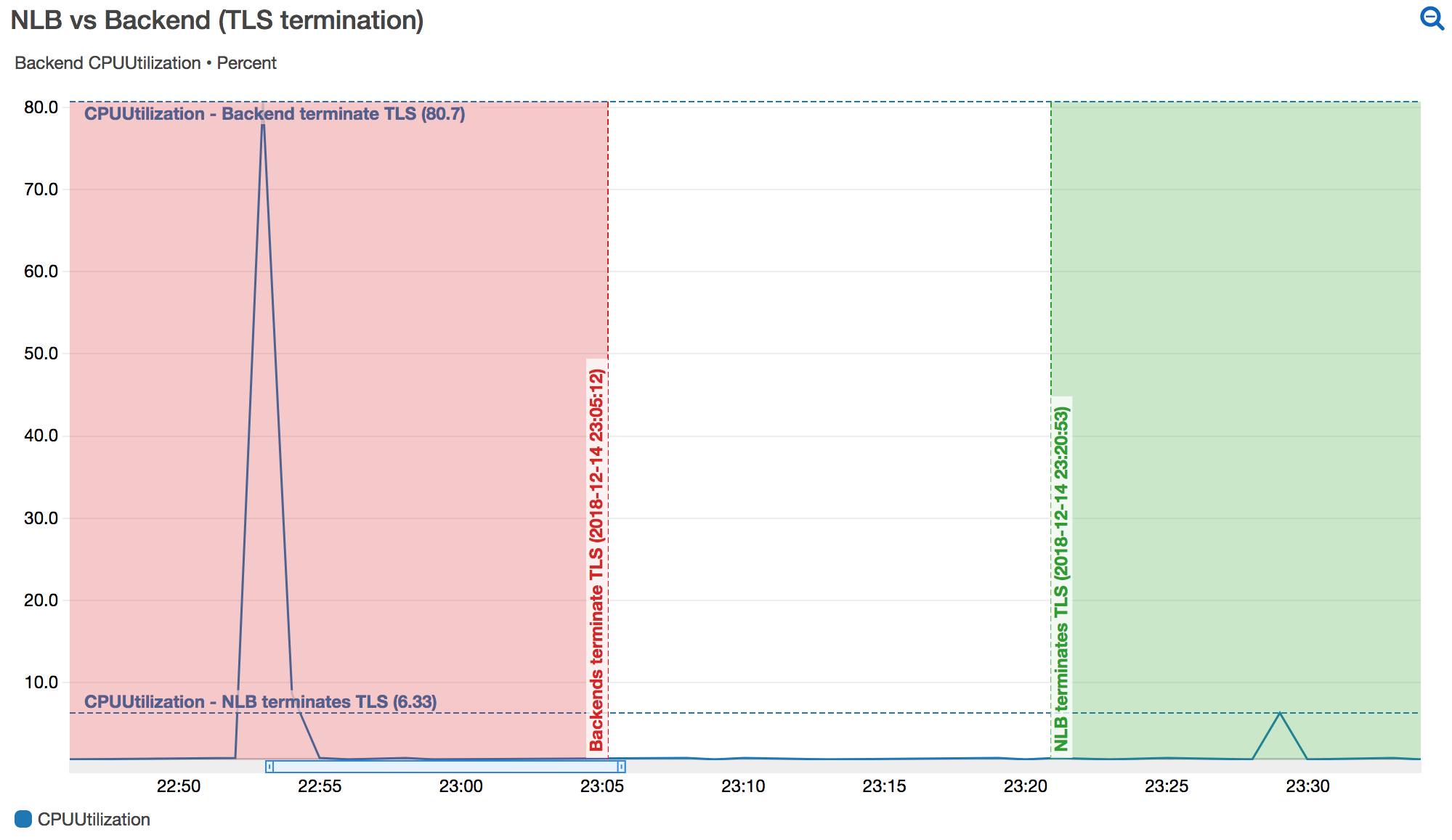
We performed a test to help understand how much extra capacity we need to provision our backend application just for TLS termination. In our test, the client generates 1000 TLS connections/second. To keep the test simple, we decided to use TLSv1.2 with cipher suite -- ECDHE-RSA-AES256-GCM-SHA384 (2048-bits RSA certificate). In the first test (Red), the client connected to the EC2 instance directly through TLS. In the second test (Green), we registered the same EC2 instance behind a Network Load Balancer that terminated TLS connections.
As it is illustrated in the metric above , the CPUUtilization of the EC2 instance went up to over 80% in the first test; while the CPUUtilization was only around 6% in the second test, where our Network Load Balancer terminated TLS connections.
We also have cats
